Most security issues don’t begin with something obvious. It could be a small gap. Maybe a system wasn’t updated. Maybe access controls were too loose. Then, before anyone notices, that gap turns into a real problem.
This is something many partners and resellers are seeing more often. Threats are getting sharper, and in many cases, faster than internal teams can respond. Because of that, having tools alone is no longer enough.
What matters more now is how everything works together. That’s where cybersecurity posture becomes important. It reflects the overall state of security across systems, users, and processes. Instead of relying on assumptions, businesses can lean on a proper security assessment and stronger risk management security practices.
BluechipIT supports partners in this space by helping them deliver more structured and practical security outcomes.
So in this blog, we’ll walk through what cybersecurity posture really means, why it matters in 2026, and how partners can help improve it through better security risk management.

What Is Cybersecurity Posture?
If you strip it back, cybersecurity posture is simply a way to describe how secure an organisation is at any given time.
It’s not based on a single tool. Instead, it looks at how different parts come together.
For example, policies set the direction. Tools help detect and prevent issues. Processes guide how teams respond. Then you have people, who manage and maintain everything daily.
When one of these areas is weak, the whole setup feels it. On the other hand, when they align, the environment becomes more resilient.
This is also why cybersecurity posture is closely linked to any security and risk assessment. Without visibility, it’s difficult to know where improvements are needed.
Why Cybersecurity Posture Matters in 2026
The pace of cyber threats has changed. Attackers are no longer working slowly. Many now rely on automation, which allows them to scan for weaknesses at scale. At the same time, the impact of a breach keeps rising. According to IBM’s 2024 Cost of a Data Breach Report, the average cost reached USD 4.45 million.
That number alone shows why reactive security no longer works. There’s also increasing pressure around compliance. Businesses are expected to show that they are actively managing risks. Without ongoing security risk management, that becomes difficult to prove.
For partners, this creates a shift. Customers are not just asking for products anymore. They want guidance. They want support around cyber security assessment, visibility, and long-term protection.
If you’re looking to support your customers more effectively, BluechipIT provides structured security assessment services that make this easier.
👉 Get your assessment score now >
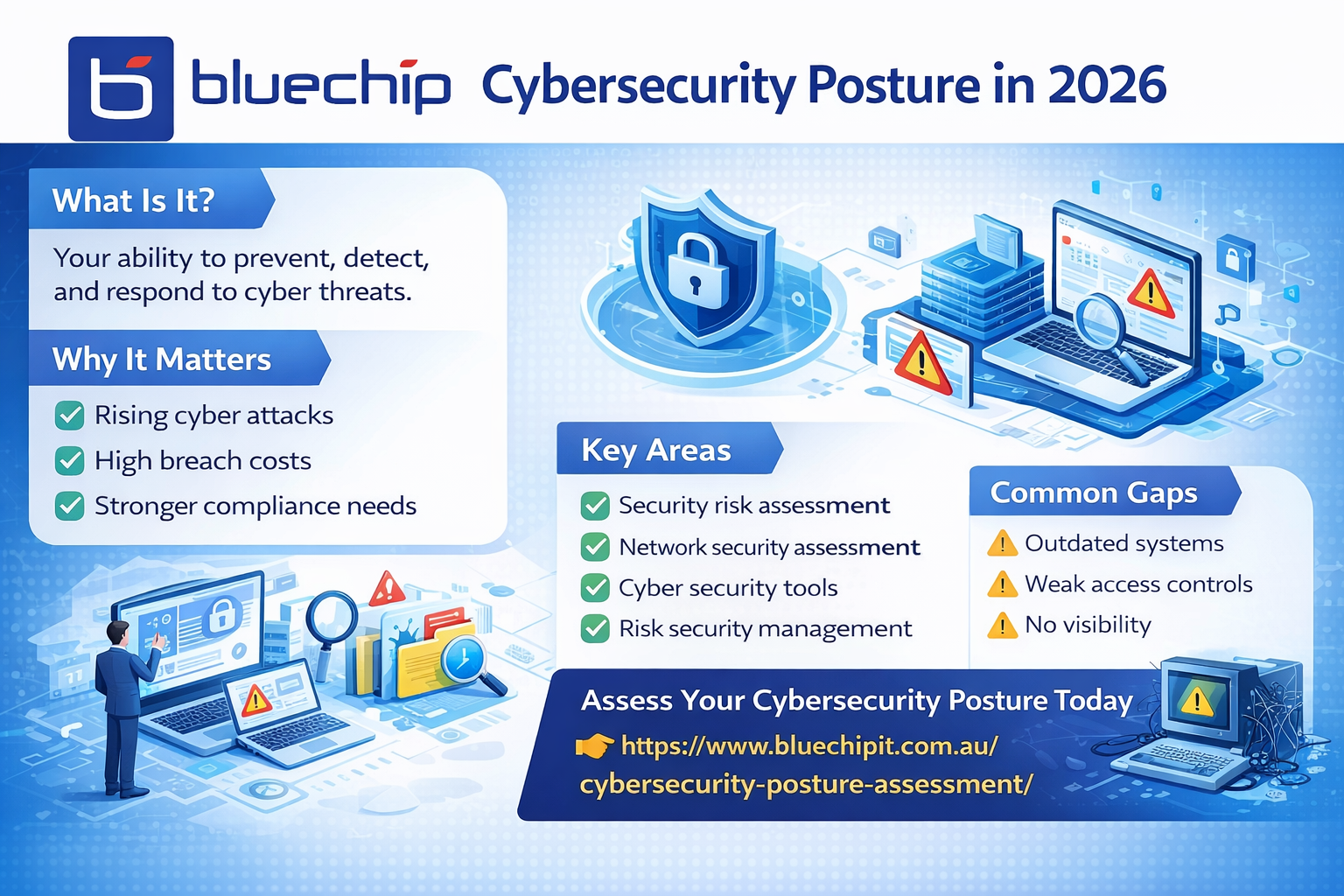
Key Components of a Strong Cybersecurity Posture
Security Risk Assessment
Everything usually starts here. A security risk assessment highlights where the real issues are. Instead of guessing, businesses get a clearer view of vulnerabilities.
A security risk assessor helps translate that into practical actions, which makes prioritisation easier. This also strengthens overall risk security management by ensuring risks are properly identified early.
Network Security Assessment
Then there’s the network side. This often gets overlooked, yet it carries a lot of risk.
A network security assessment looks at traffic patterns, configurations, and access points. With better visibility, unusual behaviour stands out faster. That alone can reduce response time significantly.
Cyber Security Assessment Tools
Manual reviews can only go so far. That’s why many organisations now rely on a cyber security risk assessment tool.
These tools provide continuous insight rather than one-off snapshots. They also help reduce manual effort, which frees up teams to focus on higher-value tasks.
Risk & Security Management Frameworks
Without structure, even good tools fall short. This is where risk & security management frameworks come in.
They help connect assessments, actions, and outcomes. A security and risk manager typically oversees this, making sure everything stays aligned with business needs.
Cybersecurity Posture vs Security Risk Assessment
It’s easy to mix these two up, but they serve different purposes. Cybersecurity posture reflects the overall condition of security. It answers a broad question: how prepared are we?
A security risk assessment, on the other hand, focuses on identifying specific risks. It’s more targeted. Both are necessary. In practice, regular security and risk assessment helps improve posture over time.
Common Gaps in Cybersecurity Posture
Even businesses that invest in security can have blind spots. Some still run outdated systems. Others struggle with limited visibility across their environment. Access controls can also become too broad, especially as teams grow.
Another issue is inconsistency. Without a clear security risks management approach, improvements tend to happen in silos. Over time, these gaps add up.
How to Improve Your Cybersecurity Posture
There’s no single fix, but there are clear starting points. Regular cyber security assessment helps keep risks visible. It also prevents small issues from being ignored. At the same time, strengthening network security assessment practices improves detection.
When something unusual happens, teams can act sooner. Tools also play a role. A well-chosen cyber security risk assessment tool can simplify monitoring and reporting. Beyond that, focus on risk management security as a whole. The goal is to align people, processes, and technology.

How BluechipIT Helps Strengthen Cybersecurity Posture
For many partners, the challenge isn’t awareness. It’s execution. BluechipIT helps bridge that gap. Their approach focuses on clarity and practical outcomes rather than unnecessary complexity.
Partners gain access to comprehensive security risk assessment services, along with expert guidance. This makes it easier to deliver consistent results. In turn, it strengthens their overall risk management security offering.
Conclusion
Cybersecurity posture is no longer just a technical concept. It has become a key part of how businesses operate and grow.
As threats continue to evolve, staying reactive is no longer enough. A more structured approach to security risk management is needed.
For partners and resellers, this is a chance to step in with real value. By helping customers improve their security and risk assessment strategies, you also build stronger, long-term relationships.
Assess Your Cybersecurity Posture Today
Give your customers a clearer view of their risks and practical steps to improve.
