Security used to be simpler. A firewall and antivirus were often enough. That is no longer the case. Today, threats move faster, and environments are more complex. MSPs now manage multiple clients, each with different risks and requirements. At the same time, expectations continue to rise.
End customers no longer settle for basic protection. They expect strong, reliable security that feels seamless. However, many MSPs still rely on disconnected tools that do not fully work together. This often leads to gaps, delays, and unnecessary complexity.
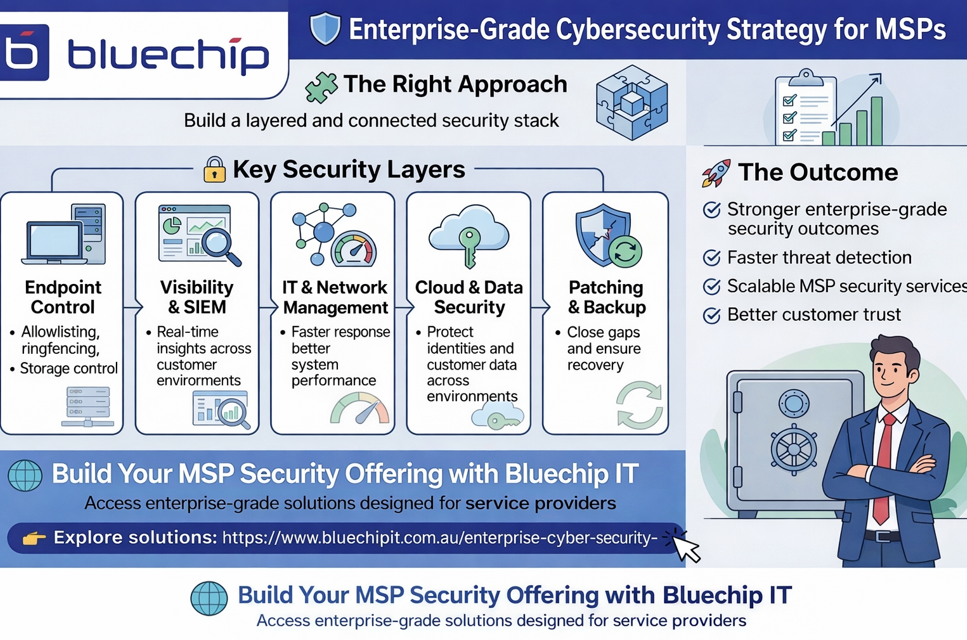
This is where the challenge begins. It is not always about lacking tools. It is about lacking structure. A well-designed MSP network security stack should feel connected. Each layer should support the next. When everything works together, security becomes easier to manage and scale.
Bluechip IT works with partners as a cybersecurity distributor, helping deliver enterprise-grade solutions that MSPs can use to secure and manage their customers’ environments. In this blog, we will explore how to build a practical and scalable enterprise cybersecurity strategy designed specifically for MSP service delivery.

Why MSPs Need an Enterprise Cybersecurity Strategy
Threats are not slowing down. If anything, they are becoming more frequent. The Australian Cyber Security Centre (ACSC) reported that a cybercrime is logged every 6 minutes in Australia. That statistics highlight the reality MSPs face daily.
End customers now expect MSPs to deliver enterprise-grade cybersecurity services, even across diverse and complex environments. At the same time, compliance and data protection requirements continue to grow.
However, many managed IT service providers still stack tools without considering how they integrate. Over time, this creates confusion. Alerts get missed, and response times slow down.
Instead of adding more tools, MSPs need a clear enterprise cybersecurity strategy. One that focuses on how solutions work together, beyond just basic firewall & network protection.
Core Layers of an MSP Security Stack
For MSPs, these solutions are not used in isolation. They form part of a broader service model, allowing providers to manage and secure multiple customer environments efficiently.
Endpoint Security & Control
Most attacks still begin at the endpoint. A single click can create a serious issue. That is why strong endpoint control is essential.
ThreatLocker uses allowlisting to ensure only approved applications can run. This approach reduces risk significantly. In addition, ringfencing limits how applications behave, while storage control manages how data moves.
Together, these controls help MSPs prevent threats before they execute across customer environments.
SIEM & Visibility
Without visibility, security becomes reactive.
Splunk Enterprise Security helps MSPs centralise data across environments. A well-structured Splunk dashboard makes it easier to identify unusual activity. Splunk observability adds deeper insight into system performance and behaviour.
With better visibility, MSPs can detect threats earlier and respond more effectively across multiple clients.
IT Service & Network Management
Security and operations are closely linked.
ManageEngine ServiceDesk Plus supports structured workflows and incident management. This helps teams stay organised and respond quickly.
At the same time, network management ensures stability across environments. When systems run smoothly, security tools perform better.
For MSPs, this improves both service delivery and security outcomes.
Looking to build a stronger MSP security stack? Visit Bluechip IT and explore enterprise-grade solutions designed for service providers.
Cloud & Data Security
Cloud adoption continues to grow, and so do the risks.
Entrust focuses on cloud infrastructure security and data protection services. It helps secure identities, transactions, and sensitive information.
For MSPs, this means better control over customer environments and protected information across multiple tenants. It also supports privacy and confidentiality requirements in regulated industries.
Endpoint Management, Patching & Backup
Some of the biggest risks come from small gaps. Missed updates, outdated systems, and failed backups can all lead to serious issues.
NinjaOne simplifies patch management by automating security updates. This ensures systems remain protected without constant manual effort.
Backup services also provide a critical safety net. Whether using online backup services or cloud backup services Australia, MSPs can ensure fast recovery for their clients.
This layer plays a key role in maintaining business continuity.
How Resellers Can Build a Scalable Security Stack
There is no single approach, but there are clear starting points.
First, MSPs need to understand each client’s risk profile. This helps prioritise the right solutions.
Next, align tools across key layers such as endpoint, network, and cloud. Keep the structure simple and repeatable.
Integration should remain a priority. When tools work together, operations become more efficient.
MSPs are not just deploying tools. They are building scalable services. Many cyber security reseller partners also standardise their offerings, making it easier to support multiple clients without increasing complexity.
The Role of a Cybersecurity Distributor
Choosing the right cybersecurity distributor can make a significant difference.
Bluechip IT connects partners with leading vendors such as ThreatLocker, Splunk, ManageEngine, Entrust, and NinjaOne. More importantly, we help MSPs translate these technologies into practical, service-ready solutions.
This includes technical support, enablement, and access to training such as Splunk certifications.
With the right support, MSPs can deploy solutions faster and deliver consistent services across their customer base.
Common Gaps in MSP Security Stacks
Even well-established MSPs can face gaps.
Some rely too heavily on firewall & network protection. Others lack proper endpoint control. Visibility may also be limited without a SIEM solution in place.
Inconsistent patching creates additional risk. Backup strategies are sometimes overlooked until an issue occurs.
These challenges are common, but they can be addressed with a more structured approach.

Future-Proofing Your MSP Security Strategy
Cybersecurity will continue to evolve. Automation is becoming more widely used. AI is starting to support threat detection and response. Identity-based security models are also gaining importance.
Zero Trust remains a key approach. It focuses on verifying every action rather than assuming trust. At the same time, MSPs are moving away from siloed tools. Integrated platforms are becoming the standard for delivering enterprise IT security at scale.
Conclusion
Building a strong MSP network security stack is not about adding more tools. It is about creating a connected and scalable strategy.
By focusing on integration and structure, MSPs can deliver enterprise-grade cybersecurity services to their customers in a consistent and manageable way.
This approach not only improves protection but also helps MSPs grow their service offerings and build long-term client trust.
Build a Stronger MSP Security Stack
Deliver enterprise-grade cybersecurity services with confidence. Support your clients with solutions that scale and integrate
